Easily enforce controls for sharing, permissions, membership, and configuration. All your workspaces, completely secure.
Policies makes it easy to automate common rules for access, settings, and other configurations. Set white/black list policies, policies for external sharing, and more. When Policies catches configuration drift, notify and even revert the change automatically. Securing collaboration in Teams, Groups, Sites, and OneDrive has never been easier.
Policies helps you monitor and enforce compliance with Office 365 security and configuration rules and best practices. AvePoint keep admins focused on what matters. Proactively manage access, white/black list, sharing, and even version controls for your Teams, Groups, Sites, and OneDrives. You define the rules – and AvePoint do the rest.
Create rules that map to your business needs.
Configure rules for access, sharing, tagging, versions, and more.
Easily monitor rule, best practice, or policy compliance.
Easily enforce security and compliance policies for permissions and access controls – including for external users. Automatically detect, notify, and revert configuration drift and security issues. AvePoint data pulls directly from Microsoft 365 security, activity, and compliance feeds. So, AvePoint doesn't over-load your tenant with crawls! That means policies for membership and access can be easily enforced as you grow.
Build policies based on insights and best practices to enforce your tenant guidelines.
Revert or notify of configuration drift and security issues automatically.
Built to scale – so you can get insights and apply batch fixes in record time.
When paired with Insights, dashboards prove progress, so you can understand how well issues are being addressed. Demonstrate reduced risk for key stakeholders, to prove PI’s value to the business.
Time-based security dashboards demonstrate business impact of administrative actions.
Track your risk score over time to demonstrate your Microsoft 365 security posture.
Centrally audit admin activity to track improvements across Teams, Groups, SharePoint, and OneDrive.
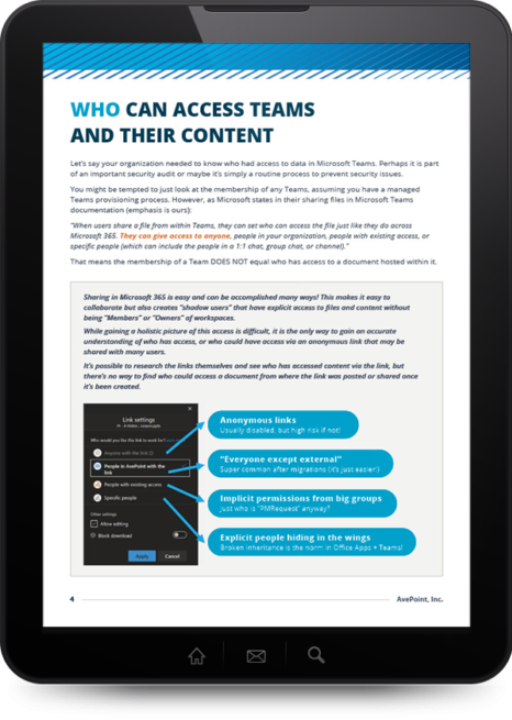
When it comes to understanding potential data exposures, IT admins are weighed down by manual, time-consuming processes that don't even tell the full story. As Teams usage continues to rise, IT admins must have a deep understanding of their organization's data ecosystem. Find out how to identify risks and design a control plan to make Microsoft Teams smart, safe, and simple for your users.
Drive IT Efficiency
For IT Directors
Built-in best practices and automated controls take the complexity out of configuration. Focus on higher-value projects while Policies takes care of the rest.
Reduce Risk
For Security Officers
Automation ensures consistent policy implementation. Get the insight you need, fast, to prove compliance with access rules and information barriers.
Increase ROI
For Business Owners
Improve productivity with the latest collaboration tools. Security features are baked in so you can focus on driving maximum business results.
Not sure which policies and rules make sense for you? Get Insights, and get the insight you need to build better policies. Insights uses Microsoft’s own data, so AvePoint is not crawling Microsoft 365, or adding to your throttle concerns. AvePoint do the dirty work of combining, parsing, and prioritizing your potential issues – so you don’t have to! How else will you know what rules are most critical? Admins can stay focused on what matters most.
External User Management
Easily monitor, control, and set access policies for external users, tailored for workspace purpose or metadata.
Automated Policy Enforcement
Ensures user actions will not violate content and security rules by automatically reverting out-of-policy changes in Microsoft 365.
Reclaim Licenses
Remove or downgrade the license of disabled or inactive users with Cense integration.
Create Your Own
Use default templates to quickly create new policies with recommended rules to control sensitivity, external sharing, data protection, and license usage.
Get a Head Start
Choose from more than 30 out-of-the-box policies which can be quickly configured, selectively applying rules to workspaces based on context, such as metadata or sensitive information types.
Fast & Frequent
Alert and revert out-of-policy changes as often as every two hours, accessing and repairing violations with just a few clicks.